Age verification is a vital process in today’s digital ecosystem. It ensures that only eligible individuals access age-restricted content and services—helping businesses stay compliant while protecting minors from harmful or inappropriate material.
As digital platforms expand, traditional “show your ID” methods are no longer practical. Online businesses must adopt secure, scalable, and privacy-conscious digital verification systems to meet growing regulatory demands and consumer expectations.
What Is Age Verification and Why It Matters
Age verification confirms that a user meets the legal age requirement for specific goods, services, or content. It’s a legal and ethical safeguard used by industries such as:
-
Alcohol and tobacco sales
-
Online gaming and gambling
-
Adult entertainment
-
Vaping and cannabis products
-
Financial and dating platforms
Why It Matters
-
Legal compliance: Prevents fines, penalties, and legal exposure.
-
Protection of minors: Keeps age-inappropriate content or substances inaccessible.
-
Consumer trust: Demonstrates corporate responsibility and transparency.
-
Fraud prevention: Reduces misuse of identities or accounts by underage users.
A well-implemented age verification system not only protects your audience—it reinforces brand credibility and compliance readiness.
Legal and Regulatory Frameworks for Age Verification
Age verification is no longer optional—it’s a legal necessity across many regions. Governments and regulators worldwide have introduced frameworks requiring digital businesses to confirm a user’s age before granting access to restricted content, products, or services. These measures aim to protect minors, uphold privacy, and ensure ethical digital practices.
While the underlying goal is consistent—to prevent underage access—specific regulations vary by region. Understanding these requirements helps businesses stay compliant and avoid severe financial or reputational penalties.
United States
In the U.S., age verification is governed by a combination of federal and state-level laws:
-
Children’s Online Privacy Protection Act (COPPA): Requires online services directed at children under 13 to obtain verifiable parental consent before collecting any personal information.
-
State-Specific Regulations: Many states have introduced additional rules for alcohol, tobacco, vaping, and adult content. For instance, states like Utah and Louisiana have enacted laws mandating digital age verification for access to adult content sites.
-
Emerging Trends: Expect continued expansion of state-level online safety and privacy laws mirroring Europe’s stricter frameworks.
United Kingdom
The UK has implemented some of the world’s most comprehensive digital safety regulations:
-
Digital Economy Act (2017): Mandated strict age verification checks for adult content websites. Although implementation was delayed, it set the foundation for modern standards.
-
Online Safety Act (2023): Overseen by Ofcom, this legislation enforces proactive measures by online platforms to prevent minors from accessing harmful or age-inappropriate content. Ofcom now holds enforcement authority, empowering it to fine or restrict non-compliant services.
-
Key Requirement: Platforms must demonstrate “proportionate and effective” age assurance systems that protect both children and user privacy.
European Union
The EU has taken a privacy-first but increasingly rigorous stance on digital age verification:
-
GDPR (General Data Protection Regulation): Imposes strict controls over personal data collection, requiring that age verification systems minimize data usage and ensure consent transparency.
-
Audio-Visual Media Services Directive (AVMSD): Requires online video platforms to protect minors from harmful content through effective age checks and parental control mechanisms.
Country-Specific Regulations
-
Germany: The Jugendschutzgesetz (Youth Protection Act) mandates verified age checks for online content classified as harmful to minors. The KJM (Commission for the Protection of Minors in the Media) certifies compliant verification systems.
-
France: The ARCOM authority enforces regulations requiring adult websites to block access to minors through verified, privacy-compliant age verification mechanisms. Heavy fines apply for failure to comply.
-
Italy: The AGCOM (Italian Communications Authority) enforces rules under its digital media framework requiring platforms to implement parental controls and age restrictions for explicit or harmful content.
Across the EU, enforcement is intensifying, and businesses are expected to use secure, data-minimizing technologies that meet both national and EU-wide compliance standards.
Asia and Emerging Markets
Many Asian countries have adopted SIM-based age verification, leveraging national ID-linked mobile phone registrations. Since mobile SIM cards are often tied to verified identity documents, they serve as a de facto age confirmation method.
Examples:
-
Japan and South Korea: Require mobile carriers to verify the age of users purchasing SIM cards or registering online services.
-
Singapore: Uses SingPass-linked identity systems to confirm age for government and private digital services.
-
India and Indonesia: Require telecom verification (KYC) for SIM issuance, indirectly enforcing age validation.
These SIM-based systems are effective at scale but raise concerns about data privacy and user anonymity—areas where privacy-first solutions like tokenized verification (e.g., AgeWallet™) offer a balanced alternative.
Global Compliance Outlook
Globally, regulators are shifting toward privacy-conscious, technology-driven verification systems that minimize personal data exposure. Businesses operating across borders must adopt flexible solutions capable of meeting different regional standards—balancing compliance, privacy, and user convenience.
Implementing a compliant, adaptive verification process is no longer just a legal safeguard—it’s a competitive advantage in a world increasingly prioritizing digital responsibility.
Traditional IDs in Modern Age Verification (On-Site & Online)
Government-issued IDs remain the gold standard for proving age—and they’re usable both offline and online when paired with digital verification technology.
Common Traditional IDs
-
Driver’s license
-
Passport
-
National ID card
How They Work Online
-
Document capture & OCR: Read data from the ID (front/back, MRZ, PDF417 barcode).
-
Authenticity checks: Hologram/UV pattern analysis, font/layout templates, tamper detection.
-
Chip/NFC reading (where supported): Read e-passport or eID chip data to confirm integrity.
-
Selfie + liveness: Match the face on the ID to a real, present user (active/passive liveness).
-
Issuer/database validation: Cross-check number formats or status against trusted sources.
-
Standards-aware flows: e.g., ICAO 9303 MRZ, AAMVA barcode formats (U.S.), ISO/IEC 18013-5 mobile driver’s license (mDL).
Strengths
-
High assurance: Strong link to a real person and verified age.
-
Regulator-preferred: Often the clearest path to compliance.
-
Fraud controls: Multi-signal analysis (document security + selfie + chip) dramatically reduces spoofing.
Limitations (to Manage, Not Avoid)
-
Privacy & data minimization: Collect only what’s needed for age; store securely and briefly.
-
Friction: Mitigate with guided capture, auto-crop, and real-time feedback.
-
Coverage variances: Not all IDs or chips are equally readable across regions/devices.
Recommended Best Practices
-
Add selfie+liveness for presence and face matching for anti-spoofing.
-
Use data minimization: Extract only “18+ pass” confirmation, not full PII.
-
Offer fallbacks by region: e.g., SIM/KYC where common, but never as the sole method if regulators require ID.
-
Log outcomes, not documents: Store a signed proof or token (like AgeWallet™) instead of raw ID images.
-
Re-check periodically for long-term or subscription-based accounts.
Digital and Online Age Verification Solutions
As commerce and content consumption have shifted online, digital age verification has become essential for compliance, safety, and user trust. Modern systems enable real-time validation that balances security, speed, and privacy—helping businesses meet global regulatory standards without creating user friction.
Core Digital Verification Methods
1. Document Upload and OCR Validation
Users upload a photo or scan of a government-issued ID. The system uses Optical Character Recognition (OCR) and AI-driven authenticity checks to extract and validate data such as:
-
Date of birth, name, and ID number
-
Machine-readable zones (MRZ) and barcodes
-
Holograms, microtext, or chip data (for ePassports/eIDs)
Advanced systems cross-check these details against issuing authority templates or global ID libraries to detect tampering, duplicates, or forgeries in real time.
Advantages: High accuracy and regulatory acceptance
Challenges: Requires privacy safeguards and explicit user consent
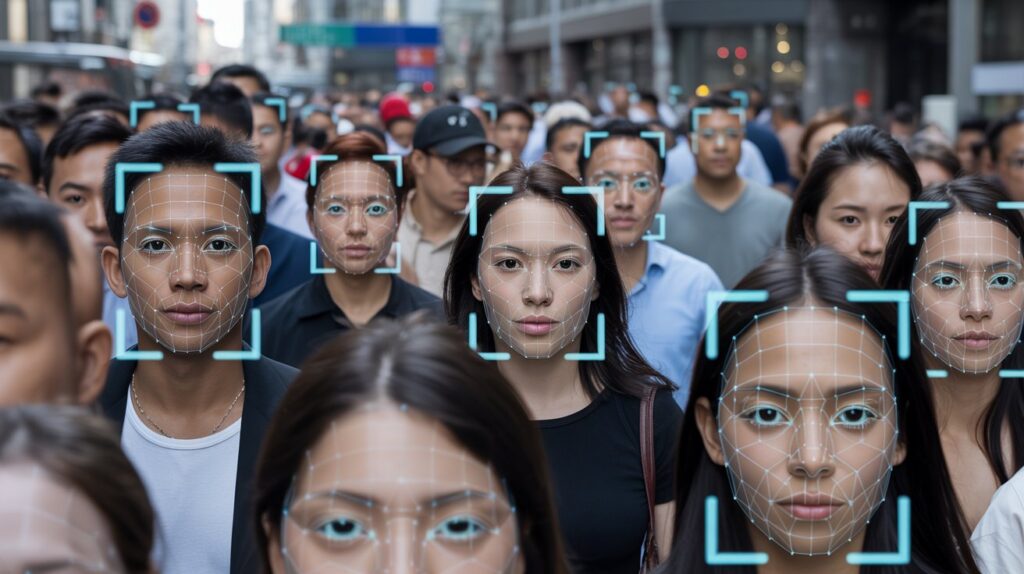
2. Biometric Verification and Liveness Detection
Biometric verification uses facial recognition and liveness detection to confirm that the user is real and matches their submitted ID. AI analyzes micro-movements (blinking, head turns) or infrared depth scans to prevent spoofing.
Use Cases:
-
Verifying identity consistency with submitted ID photos
-
Real-time camera checks for adult or gaming platforms
-
AI-powered age estimation when ID is unavailable
Advantages: Fast, secure, and highly resistant to fraud
Challenges: Must comply with biometric data laws (e.g., GDPR, Illinois BIPA)
3. Database and API Cross-Checks
These systems verify a user’s claimed age by referencing trusted third-party databases, such as:
-
Credit bureaus
-
Government registries
-
Mobile carrier KYC records
-
Telecom SIM registration databases (especially in Asia)
Advantages: Quick verification without document uploads
Challenges: Limited cross-border accessibility and potential data-sharing restrictions
4. Token-Based and Decentralized Verification
Solutions like AgeWallet™ use tokenized or cryptographic proofs to confirm age eligibility without exposing personal data. After one verification (via ID or biometric), users receive a renewable digital age token they can reuse across platforms.
Advantages: Reusable, anonymous, and privacy-preserving
Challenges: Requires industry adoption and interoperability among platforms
Other Emerging Digital Methods
-
Mobile SIM-Based Verification: Popular in Asia; confirms age through carrier records linked to verified IDs.
-
eID & Digital Wallet Integration: Countries like Germany and Singapore allow verification through national eID apps or government wallets.
-
AI Age Estimation: Used as a secondary method to flag potential minors before deeper verification.
Deprecated or Non-Compliant Methods
Older methods such as social media logins or credit card validation are not sufficient for regulatory compliance.
-
Social Media Accounts: Easily falsified birthdates; unreliable.
-
Credit Card Checks: Minors may use prepaid or shared cards; lacks certainty of cardholder age.
Regulatory Note: Businesses relying solely on these outdated methods risk non-compliance fines and reputational damage. Use them only as secondary indicators.
Website Age Verification Practices
Websites offering restricted content must integrate appropriate age verification systems tailored to their industry.
Effective Options Include
-
Seamless pop-up verification screens or landing gates
-
API integrations with trusted verification providers
-
User account creation requiring verified birthdate
-
AI-powered identity and liveness checks
A best-in-class system verifies users quickly, protects personal data, and reduces friction in the user journey.
Third-Party Verification Services
Many businesses use specialized third-party tools to streamline compliance. Providers like AgeWallet™ offer secure APIs and AI-driven systems that integrate easily with existing platforms.
Advantages:
-
Rapid implementation
-
Regular compliance updates
-
Data encryption and secure verification
-
Reduced liability through verified audit trails
By partnering with established providers, businesses can stay compliant, reduce operational risk, and maintain customer trust.
Balancing Security, Privacy, and Compliance
Age verification involves handling sensitive personal information, making robust security and transparency essential.
Best Practices
-
Encrypt data during transmission and storage.
-
Seek explicit user consent and explain data usage clearly.
-
Delete or anonymize verification data post-validation.
-
Stay compliant with data privacy laws (GDPR, CCPA, etc.).
Maintaining the right balance between effectiveness and privacy builds user trust while ensuring compliance with global standards.
The Future of Age Verification Technology
The industry is moving toward privacy-centric, interoperable verification systems that allow users to control their data. Technologies such as blockchain-based credentials, AI-enhanced biometrics, and tokenized proofs are reshaping the verification landscape.
Emerging Trends Include
-
AI and Machine Learning: Advanced liveness detection and fraud prevention.
-
Blockchain Verification: Immutable, transparent records without storing sensitive data.
-
Anonymous Tokens: Allow users to prove age without sharing personal details.
Modern age verification is no longer just about compliance—it’s about creating trustworthy, privacy-conscious digital ecosystems that protect users and strengthen brand integrity.
Key Takeaways and Best Practices
-
Choose verified, compliant methods over self-reported or easily bypassed options.
-
Update systems regularly to align with evolving global regulations.
-
Prioritize user privacy and transparency in data handling.
-
Partner with a trusted third-party age assurance provider like AgeWallet™ for reliability and faster deployment.
Robust age verification is more than a compliance requirement—it’s a commitment to protecting minors, preserving trust, and building a safer digital future.